Before you know about the cyber security challenge, you should know about cyber or web security. What is cyber security? Protecting and keeping all the cyber systems malware-free is best known as cyber security.
It includes the applications and software you use and the data you store. In the modern digital world, we are all surrounded by the cyber system and cyber threats.
The more new technologies we get, the more ways to hamper cyber protection. According to recent research nowadays, there’s a massive increment in cybersecurity challenges. Cybercriminals are being able to find new ways to escape every cyber protection. Day by day, the IT security challenges are becoming more puzzling.
Cyber Security Challenge for The Future
There are a vast number of cybersecurity challenges around us. Describing them all at once is hard. So, here, we are going to share a generic list of Cyber Security Challenges with you. I hope it helps you to know about the cybersecurity challenge.
1. Machine Learning Cyber Attack
We know that machine learning is one of the best technologies for data processing. It comes with the great ability to process a huge amount of data, detect malfunctions, and adjust algorithms.
We use it because of its amazingly increasing accuracy and faster nature. It seems to be very crucial for the data. That’s why hackers target machine learning to make it one of the cyber threats. They use its faster behavior against its cyber protection ability.
Through machine learning, hackers can attack and hack all the information before you can even discover the attack. So, basically, they are taking advantage by using it against themselves.
2. Ransomware

Another cybersecurity challenge that’s increasing greatly day by day is ransomware. We are sorry to inform you that the growth rate of Ransomware is unbelievably high. It’s truly a curse to data and web security and the respective professionals.
Now, it can easily take the highest place among the IT security challenges. It’s going to be an endless cyber challenge. This type of challenge will hack your data and help hackers blackmail you based on the information, as it will be able to encrypt all the data. It can cost you a very large amount of money.
Nothing can be worse than that. Criminals can have both your information and the money. You won’t be able to do anything against it.
3. Attacks through IoT
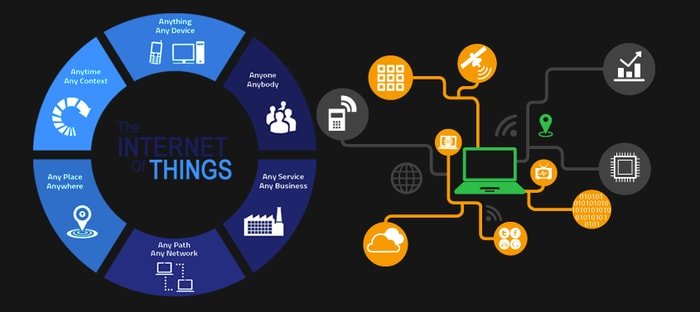
IoT – The Internet of Things is a blessing to us, but it’s an extraordinary blessing to criminals nowadays. Most of us use different types of smart devices. Thanks to IoT, we can now connect all our devices to each other, reducing a lot of complexity.
Now, you can handle and control all of your devices from anywhere using just your phone. With modern innovation, you are continuously plugged in. That’s getting you away from cyber protection. Criminals can hack one of your devices, and then they can have access to all of your information, both personal and professional.
They can use the internet of things for the DDoS attack. It will make them take down the whole system based on the internet.
4. Blockchain Hacking and Cryptojakcing

Attacks on the blockchain system are increasing, and so it becomes a headache for cyber protection. Criminals are hacking the entire blockchain system, and that’s how they are getting access to every single piece of information included in the network.
They get individual information and company data as well. Thus, spoofing or identity theft is increasing on a larger scale. They are also mining cryptocurrencies for their wallet through crypto-jacking.
There are legitimate websites where criminals can mine cryptocurrencies for the criminal wallet. The criminals make them do such mining. It’s going to be one of the top cyber threats very soon.
5. Weak passwords and Two-factor Authentication

We all use passwords in our devices and different applications for security purposes. In that case, choosing a stronger and unpredictable password is very important.
Some people use weak passwords just because they cannot remember their passwords, and it becomes a hazard for them while logging in to a particular device or application.
It becomes too easy for hackers to hack your information. The weaker the password, the easier the hacking. Now, there is an option to save the password in the browser. Though it’s secured, it won’t be hard for the criminals to get it.
Now come to the two-factor authentication process. It’s another way to hack your phone by redirecting text messages to your phone for authentication.
6. Physical Infrastructure Hacking
Cybercriminals are becoming more sophisticated with their plans to attack you. Their new target is the physical infrastructure, for example, media channels, power grid, and transportation networks. This type of cyber-attack has the potential to cause extensive disaster.
Detecting this type of sophisticated criminal is too tough for any organization, although they are trying their best. But if you have an organization, you can give this attack a place on top of your IT security challenges list. Don’t be so hopeless. There are new technologies that will help you improve your web security and save the entire infrastructure as well.
7. AI-Based Hacking
Another huge cybersecurity challenge is artificial intelligence malware. The interesting part is that it’s self-aware and can think in various ways. AI applications come with a lot of advantages, but the problem is that all those advantages come with some disadvantages, too.
AI is making our lives way easier, and it saves us time. It offers different applications which you can complete within the blink of an eye. But, once it gets corrupted, you can’t stop it from doing its task. That’s because, by the time you’re going to stop it, it will have completed all the tasks.
8. Email Phishing and Mailsploit

Emails are the most used application for any type of corporate or professional communication. People don’t just communicate but also share valuable data via email. That’s the reason criminals keep phishing emails in different ways.
This is one of their favorite tools to corrupt cyber protection. Phishing is one of the IT security challenges that are difficult enough to defend. Criminals also send malfunctioned content via fraudulent emails. They also use an exploit named Mailsploit to spoof the name of the email sender.
There are options to reduce all these phishing or spoofing. You can augment the sender representation inside the email client. You can also use an automatic smart email scanner.
9. Worm Based Malware

Using the worm is a new technique that hackers are using to spread malware. It seems that the number of hackers using worms is highly increasing. Do you know why? Because worms can compromise the network faster than any other method.
It has the ability to fast the propagation of malevolent payloads. The worm can get phishing controls, a previous firewall, and access to the core of the network. Soon, this technique is going to make a lot of people its victim.
What is cyber security? Well, the answer would be to safeguarding the information. Only one thing can prevent a worm from getting access to the data. If you store all your data in an immutable bucket, it will prevent anything from altering the data inside it.
10. PowerShell-Based Attacks

Another unrecognizable cybersecurity challenge is a PowerShell-based attack. It’s almost impossible to identify such malware. Criminals can easily escape antivirus engines. That behavior makes them more attractive to cybercriminals. There’s no need to hack the data anymore.
Criminals can control the command and control server using the PowerShell attack. The malware script can handle the device through this attack, make websites compromise, and act as proxies. It’s a different way to attack cybersecurity and have the entire control.
11. Cloud Resource Misconfiguration
Sometimes, we fail to save all of our data in our device system. We need another place to save them all or a few of them. To solve this problem, we use the cloud to store data. Both small and large companies and even individuals store data in the cloud.
Cybercriminals don’t try to steal data from the company system. Their new target in the cloud. It’s not safe to store data in the cloud anymore. Somehow they manage to get access to the particular data from the cloud.
That’s because there is a misconfiguration of permissions on the cloud resources. It’s a must to restrict permissions and access to data in the cloud.
12. Unreliable Employees
You must have learned that honesty is the best policy. Well, there are a lot of people who know it but don’t follow it. So, here comes corruption. We are talking about corrupted files, applications, and software.
However, we forgot the core issue: the corrupt personnel. Cybercriminals are way out of the league. They are criminals. We are talking about those people who act like loyal employees but are actually corrupting the cybersecurity themselves.
Such type of employee is one of the top cyber threats to every organization. Maybe, they do things like that because of their greed, frustration, or revenge. But they are the most dangerous virus to the organization and the society as well.
13. Anti-Virus Malware

We all use different anti-virus software to keep our devices free from viruses and malware. There are a lot of anti-viruses in the market. Some of them are free to download, and some need a license.
The criminals don’t even leave the anti-virus alone. They make the anti-virus malicious, and when we download it to our device, it makes our device and software malicious. It’s easier for them to hack our system using a malicious anti-virus as we definitely use one.
14. New and Advanced Technologies for Cyber Hacking

It’s true that day by day, professionals are trying harder to increase cyber protection. On the other hand, criminals are not standing quietly.
They are also becoming smarter and creating more advanced technologies for hacking. They are not leaving a single chance to create a new cyber challenge. Hacking credit card numbers and their unique codes, taping voice calls, and getting access to your phone or computer data are all old news.
Now criminals are trying to listen to what we are saying. They are using our words to make new information. You can already be the victim, but you might have no idea about it.
15. Lackings in Cyber Security Skill

Do you know what the main cybersecurity challenge is? It’s to know about the cyber protection methods. Cybercriminals are not the problem. They are doing their job. The core problem is us. We keep failing to secure cyber. There are lackings in our web security knowledge.
This thing helps cybercriminals succeed in whatever they are doing. There should be more training in web security. We should know about the different types of technology that can secure the whole cyber system.
Final Words
Cyber security is the primary concern for every single organization and also for individuals. There must be more training in cybersecurity. We must learn more about the cybersecurity challenge and the importance and awareness of cybersecurity.
Drop a comment here and let us know your thoughts and suggestions. If it is helpful, don’t forget to share it on social media.

I literally use the same password for every single thing, including my bank account. I should probably start choosing a stronger, more unpredictable password like you said. I’ll go and change a few of my passwords right now so I don’t get hacked.
Thank you for sharing the evolving trends in cybersecurity. It is important for security professionals to keep up with these latest trends to protect their networks.